Online banking frauds have been occurring more frequently than ever before. The reason? If fraud attempts are successful, they can be very lucrative for a cybercriminal. Transfers of money can be made to other accounts, or potentially converted into cryptocurrencies in order to make funds irretrievable. Fraud attempts are made easier as more online users turn to mobile banking apps, including people that are not fully aware of the dangers of the online environment. This surge in users was aided by COVID-19 pandemic lockdowns, forcing people online if they wished to continue to use banking services.
Scammers now have an opportunity to target victims while being masked by the sheer volume of global transactions that take place on a daily basis. By the time they are discovered, scammers can be long gone with their ill-gained funds. Part of the solution is for customers to employ safe digital hygiene by using strong passwords, encrypted password managers and keeping all software/apps and operating systems up to date to ensure the latest security features are applied to devices. Education about online threats posed by scam emails is also beneficial. User participation in maintaining personal security should always be encouraged, in all walks of online life. But this is just one part of the online security lifebelt.
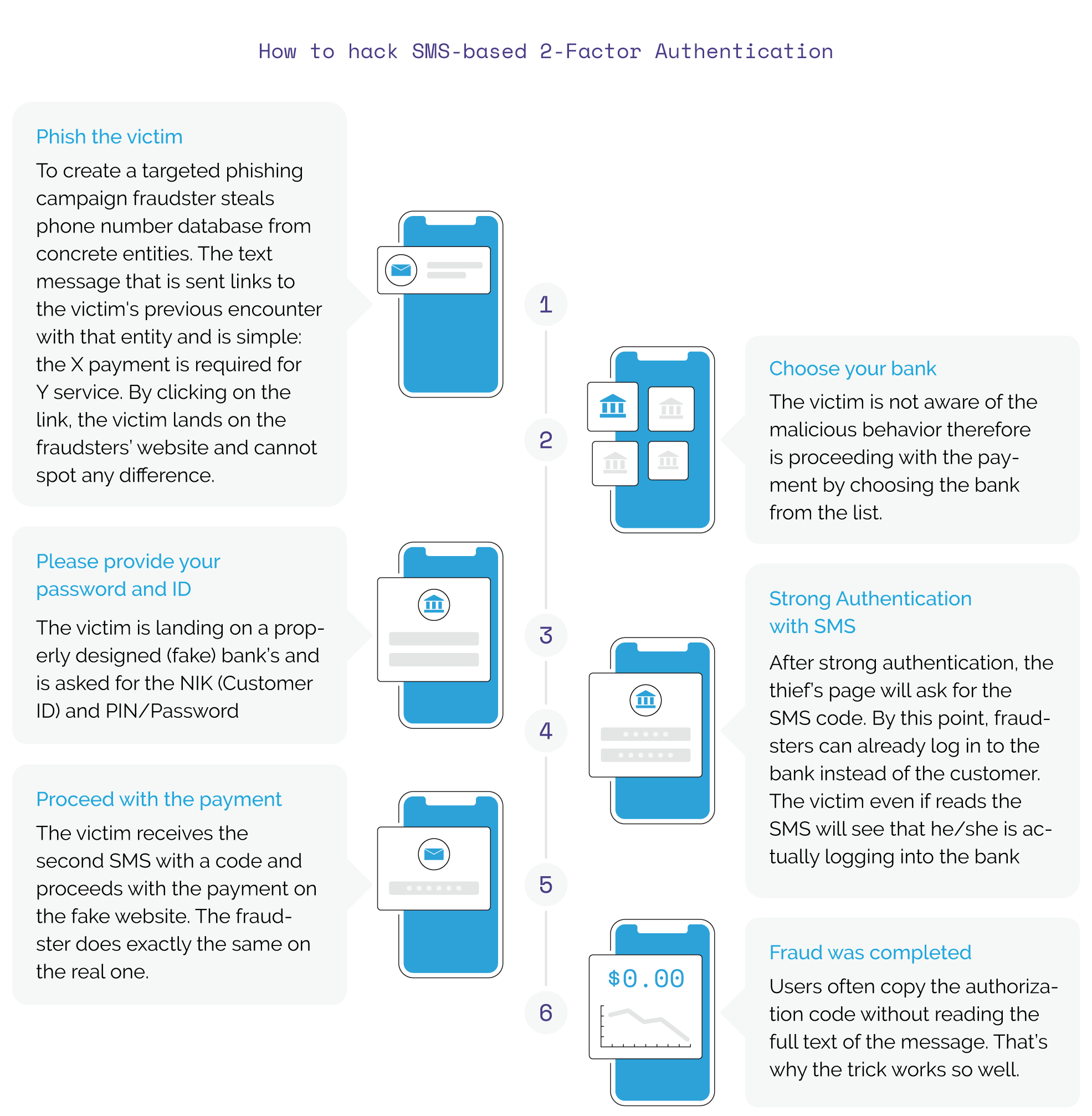
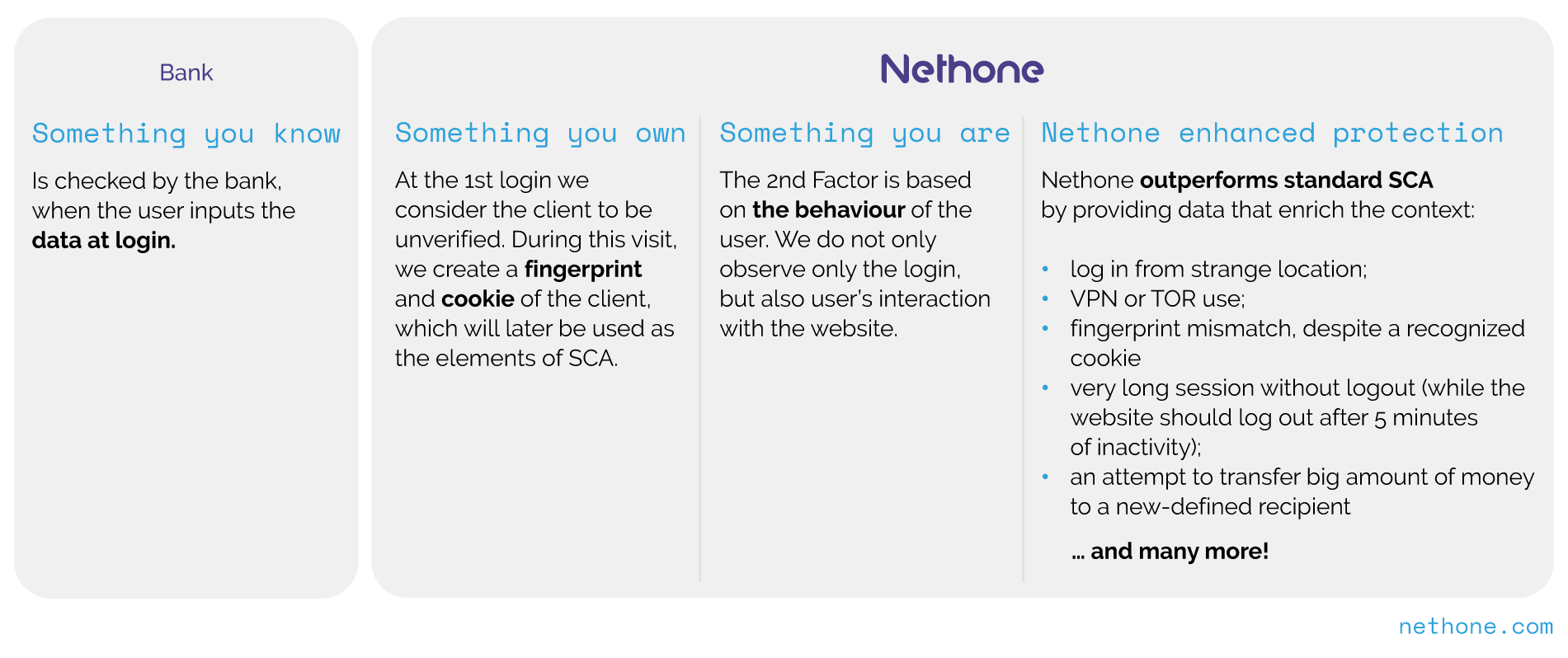
Banks too must play their part in ensuring the use of the latest fraud solutions to fight fraud. Despite FinTech companies increasing innovation and safety of online banking services, many banks still choose to send SMS as an additional layer of security in the Two-factor authentication (2FA) process. As we have previously highlighted, text messages provide neither integrity nor confidentiality of information, as seen below.