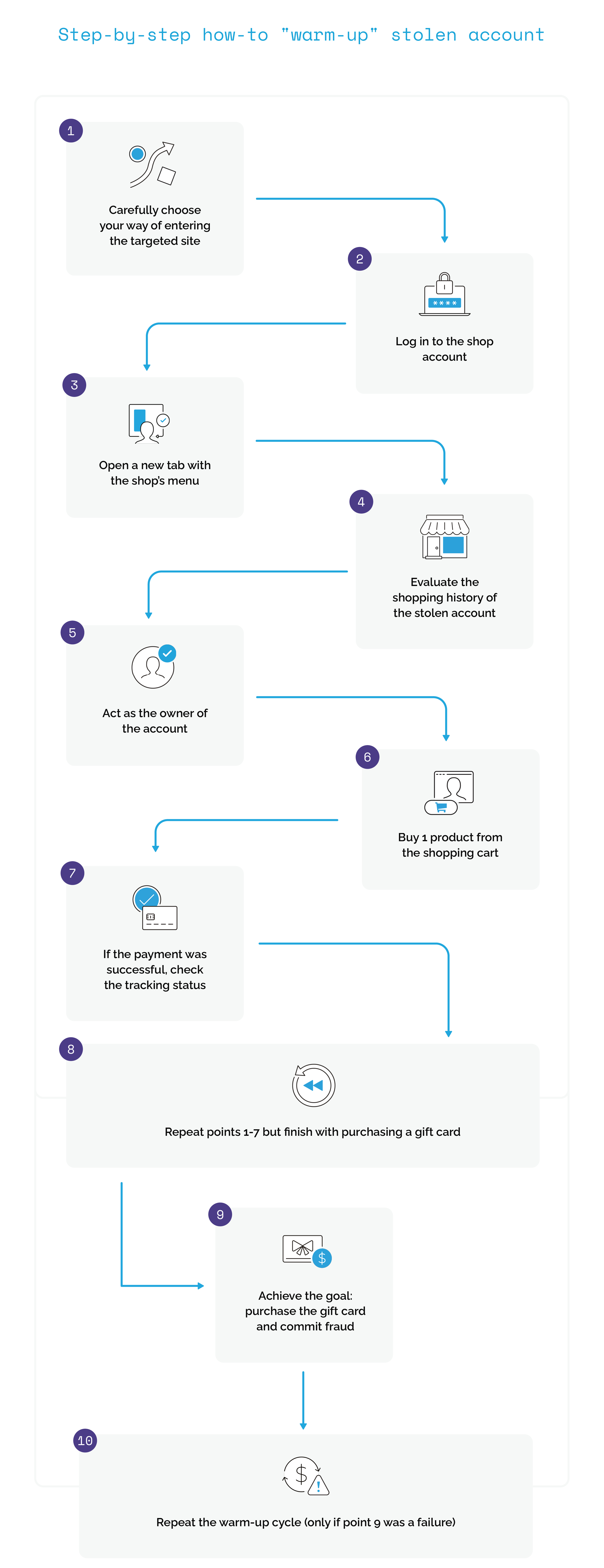
Step 1: Carefully choose your way of entering the targeted site.
Advanced fraudsters carefully choose a way of entering a target site. In this case, they enter an e-shop site directly, not through any link. They have to use a shop domain that matches the country of origin of the stolen data.
Example: If you have stolen an account/credit card/logs from Germany, you must enter the domain eshop.de instead of eshop.com. Fraudsters know that entering a shop in a different location than the user's can trigger alerts on some anti-fraud systems.
Step 2: Login to the shop account.
Type password and login.
- During account takeover fraud this is a critical moment because IF the shop has an anti-fraud system, it could be detected that there is a login attempt from a new device. Even if a new device is detected, the fraudster can still proceed with an account takeover using the account owner's email. But it’s more efficient for fraudsters to imitate victim devices using various resources (as previously mentioned) - this can be very effective if the shop doesn't use sophisticated profiling of their website users. In this case, we assume that the fraudster has imitated the victim's device successfully.
Step 3: Open a new tab with the shop’s menu.
Duplicate the shop in the browser, open a second tab with the shop menu. Go to account details and don't close this tab until the end of the process.
- This tab has to be open "in case of an emergency". During the next steps, the shop can ask for some cardholder information (like credit card expiration date, cardholder name, zip code, address, etc.). Fraudsters should have constant access to all knowledge that the account owner should know.
Step 4: Evaluate shopping history on the stolen account
Before any purchase, the fraudster should evaluate the account owner’s purchase history. A fraudster should know details about the account owner's previous orders to avoid a huge disparity between old purchases and desired items. It’s important to remember:
- the type of purchased products,
- their average value,
- shipment destination,
- payment method.
Knowing this, a fraudster will be able to copy the account owner's style of shopping.
Step 5: Act like the owner of the account.
Now it is time for one of the main parts of ‘warming up the account’. A fraudster has to check what was already bought on this account and go through recommended products, check opinions and details and then add to the basket. If it is not a stolen account but a newly registered one, a fraudster has to browse various similar products. In this step, a fraudster imitates the behaviour of a customer who contemplates as they browse the shop.
- Look at any product from the order history and click on its recommendation list. If there is no recommendation feature in a given shop, just browse the same type of product. Check its details, opinions, questions from other clients and add them to the basket. Repeat this process a few times. Each product should be viewed at random intervals. Add around 10 products to the basket. Behave like you are contemplating buying them. Discard half of them, give the remaining items further views, each in additional tabs. Spend 10-15 seconds on each product, looking again at their specifications etc.. Discard products until only 1-2 remain in the basket. At any moment during this step, a fraudster can leave it to rest for some time.
Step 6: Buy 1 product from the cart.
A fraudster will buy 1 physical product from the basket (it has to be a physical product that will be sent to the account owner's physical address). Although this is a fraudulent payment that uses a stolen credit card, the balance on a stolen account, or other pinned payment method, it is done to warm up the account. In this step, a fraudster is still acting to increase his credibility for fraud that has yet to be actioned.
- If a merchant website detects a new device, a new IP, too many changes on the account (including the most crucial, such as address and contact data updates) and purchases shipped to a new address all within a short time, anti-fraud systems or a merchant employee could recognise that something is wrong. It would be far less suspicious if a package would be sent to an old account holder’s address - the one that has been used every time. It would seem that a fraudster has no interest in shipping a fraudulent package to the account owner's home address because it would be of no gain for the fraudster. So there could be a logical conclusion that it was not a fraudulent payment but a legit transaction made by the account owner. This is the legitimization a fraudster is looking for and it will be useful for the next step.
Step 7: If the payment was successful, check the tracking status.
- Even if a payment was successful, the package could be stopped at a later step. A fraudster has to ensure that everything goes as planned and the package is on its way to the account owner's address. If everything runs smoothly they can go to the next step.
Step 8: Repeat points 1-7 but finish with purchasing a gift card.
Repeat all previous warm-up steps, but this time a fraudster’s goal will be to buy their main target - a gift card.
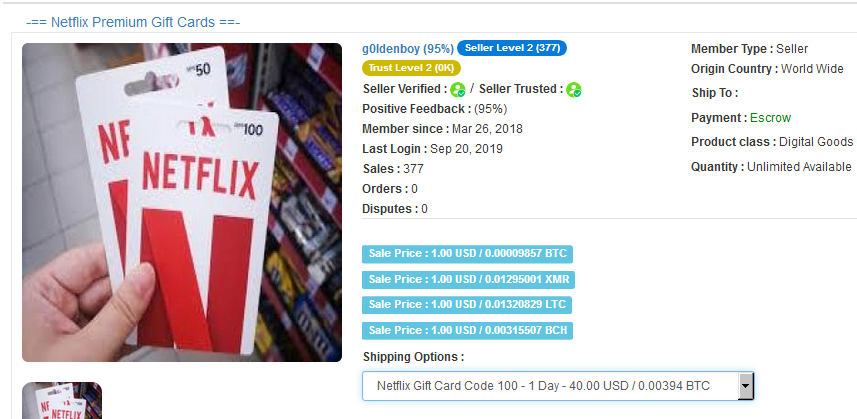
- This step consists of all previous warming-up steps starting with looking at old purchases. In this case, a fraudster wants to buy a digital gift card, and if it is possible, he should start on a product which looks similar to a gift card. If there is no similar product, a fraudster should browse for various digital products such as game keys, coupons, tickets, or various typical gift products. Using this as a way of pointing towards any gift cards, they start to browse various types of this product. There are numerous types of gift cards from different brands, so it depends on the shop assortment and a fraudster-specific goal.
In this step a fraudster goes through various products, just to end up browsing gift cards or other digital merchandise. While looking at each of these products they view its details, opinions, photos, and look at similar products. Again they add around 10 of them to the basket, among them will be a gift card that is their final goal. Each product should be viewed on a different tab. After they gather 10 products in the basket, view each of them again for 10-15 seconds and discard them. They continue this until only a gift card is left.
Step 9: Achieve the goal: purchase the gift card and commit fraud.
Fraud payment with a gift card.
- This is the next phase (final phase, below), where the fraudster commits the main part of the fraud.
Step 10: (only if point 9 was a failure): Repeat the warm-up activities
If a gift card order is not accepted, repeat the warming-up (the previous step) after 5-10 minutes. Even if the previous step was already in the new phase of the final stage of fraud, the fraudster could come back to warm up if a payment wasn’t successful.
- Giving an account a rest, in this example for 5-10 minutes, is one of the most popular warming-up techniques. Lack of patience is one of the main enemies for fraudsters because too many changes and actions on an account can raise a lot of suspicions. That’s why instead of making a second fraud attempt, the fraudster should wait for some time. Waiting more than 10 minutes wouldn’t be a mistake. After a period of rest, warming up the account for a gift card should be repeated, but more carefully. In practicality, this means looking at all products, reviews, and comments should take more time than before.