Something is rotten with the state of the Darknet
The past two months were quite difficult for the cybercrime community - something is rotten with the state of the darknet. Let's discover why?
Michał Barbaś
Intelligence SpecialistProduct
Issues we resolve
Industries
User’s Lifecycle
About
General Contact
Career Opportunities
Media Inquries
Product
Issues we resolve
Industries
User’s Lifecycle
About
General Contact
Career Opportunities
Media Inquries
The past two months were quite difficult for the cybercrime community - something is rotten with the state of the darknet. Let's discover why?
Michał Barbaś
Intelligence Specialist11 June 2019
12 min read
Reddit post from one distraught Darknet community member
Everything started at the end of March. Dream Market’s administrators announced: at this moment we can’t resist DDoS attack on our website, and we have to move to another “partner service.” Registration was closed and the information that the whole website will be shut down on April 30th was shared.
Since 2017 Dream Market has been the most prominent dark market in Darknet, where you could buy all illicit goods: drugs, stolen data, stolen credit cards, firearms, malicious software, hacking tools, access device-making equipment, and other illegal contraband.
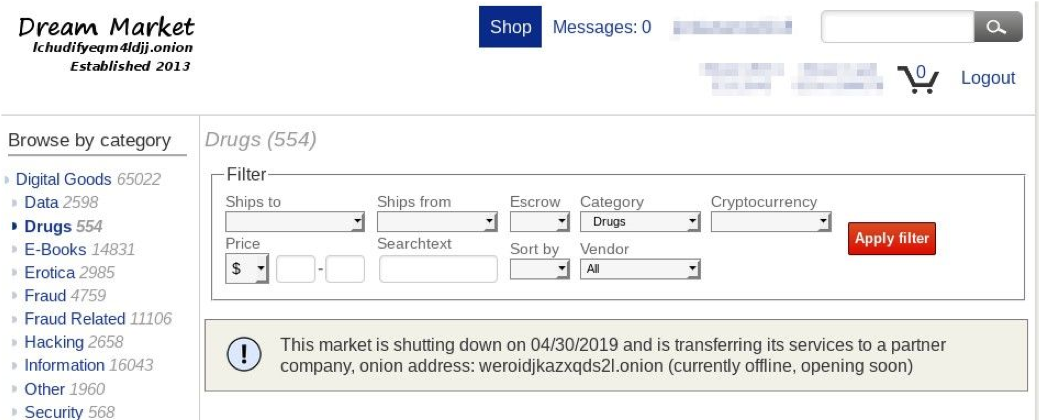
News thrilled the community because of two reasons; first, it was announced several days after the FBI released information of 61 arrests in SaboTor operation – action against dark market, especially connected with drug vendors. Secondly, Dream Market history with its moving to another server reminds AlphaBay and Hansa case from the first half of 2017.
Just to reiterate some facts from the past - AlphaBay was seized by LE in the first half of 2017. Vendors and customers had to find another big dark market. One of them was named Hansa. The clue, in that case, was that the market was already controlled by Dutch LE. For the next several months LE gathered information about new and old merchants and in July of 2017 they busted several dozens of dark markets vendors.
In the middle of April, there was another hit. This time associated with the Wall Street Market (WSM), one of the biggest dark markets in TOR. The market was available in six languages and was used by approximately 5 400 vendors and 1,15 million customers. Moreover, it offered encrypted communications between buyers and sellers. On April 16th vendors started claiming that their cryptocurrency stored in WSM was gone and administrators stopped responding to messages. Ten days later, the information about maintenance and closing the registration appeared on the market’s page. Moreover, all Bitcoins (BTC) from WSM wallet were transferred to one specific BTC wallet and from there it was distributed to other wallets. After several days the whole community was certain – WSM had employed an exit scam and stolen 11-30 million USD in BTC belonging to WSM vendors.
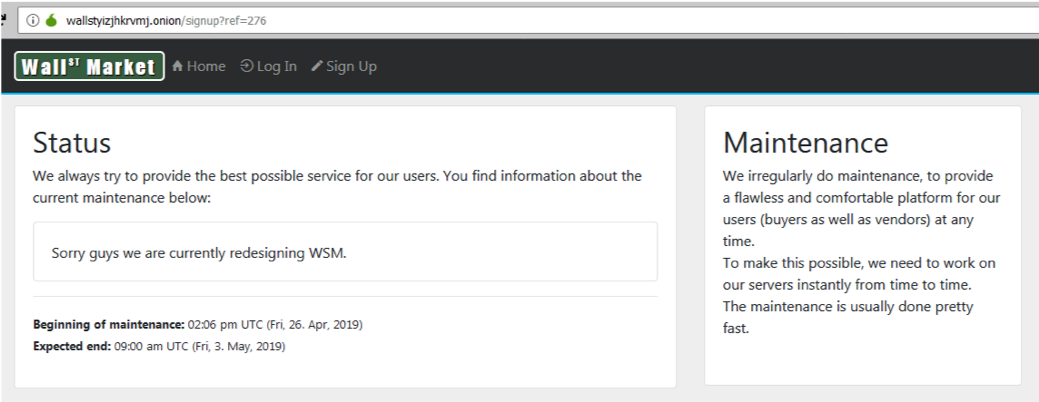
On May 2nd, everything was crystal clear, the information about maintenance on WSM website was switched by a seizure page made by German LE. According to the German Federal Police (BKA), WSM administrators were in fact, attempting an exit scam with stolen BTC. But the bad guys weren’t aware that they were already under LE surveillance. When LE understood that WSM owners would try to disappear, they arrested them. Apart from administrators, 3 other big vendors were arrested.
WSM seized by BKA:

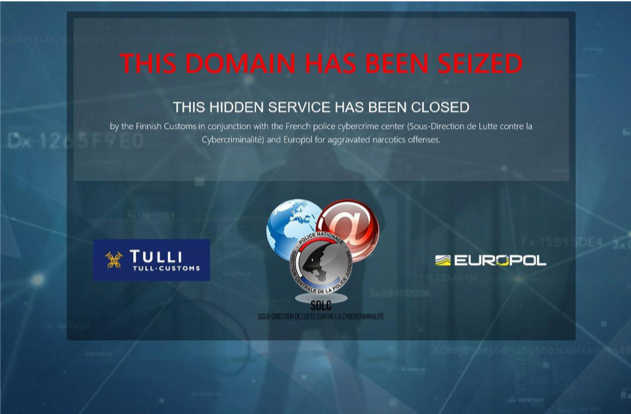
Day after BKA statement, Finnish LE and Europol announced the seizure of Vallhala. It was one of the oldest existing dark markets in TOR, as it had operated since 2013. In fact, Valhalla was closed by LE several weeks before Wall Street Market, but Europol connected both acts into one statement to emphasize LE success.
Valhalla seized by Finnish LE:
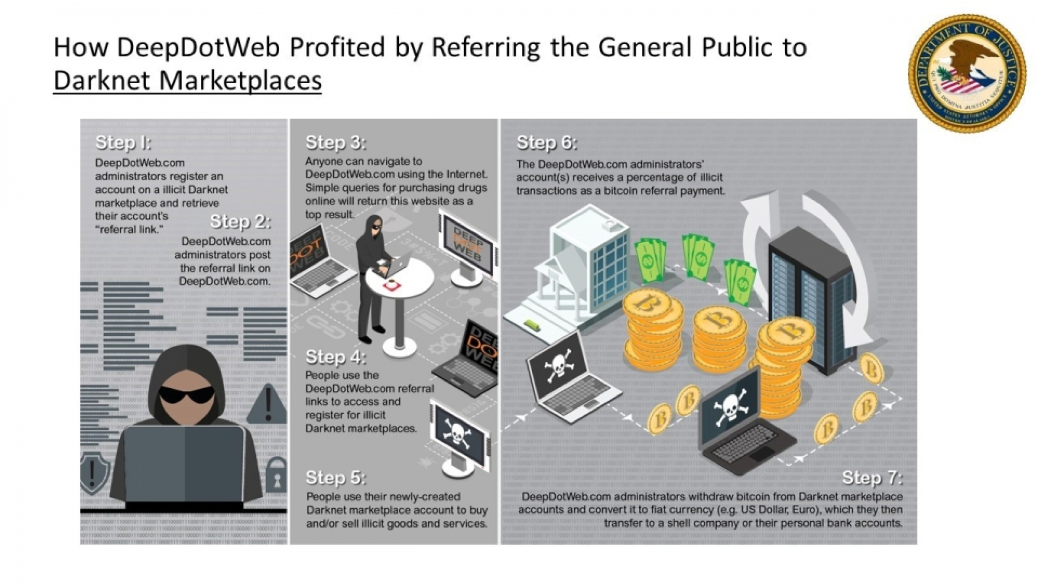
In today’s Internet, one can make money not only by selling products but also by marketing initiatives, i.e. affiliate programs. It is also present in the Darknet, but the funds you obtain are “dirty” money. Because of running such affiliate programs for dark markets, deepdotweb.com (DDW) administrators have been arrested on charges of money laundering. The website was the biggest Darknet news portal and it was accessible both in Darknet and in Clearnet (“normal” Internet available to everyone). It also contained many useful tutorials and information regarding anonymity while browsing the Internet and dark markets as well as information on their availability and functionality, and much more.
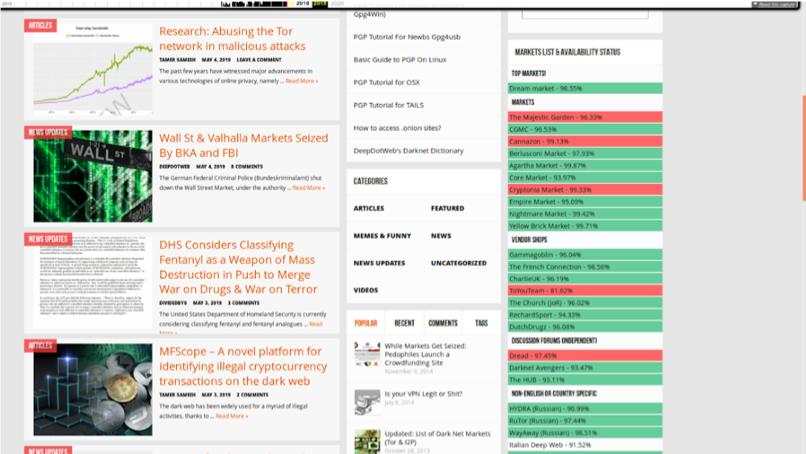
The last screenshot made by archive.org on 6th May before it was seized by LE. DDW was online since 2013. Deepdotweb earning money scheme. Source: www.justice.gov
The aspect that makes this case unusual, is the category of the website. Until now LE was seizing dark markets and forums, so it was the first case of a Darknet news portal being closed. One of the US attorneys even described this as “the first takedown of the very infrastructure that supports and promotes the illegal marketplaces where deadly drugs are sold on the Darknet.” DDW owners earned about 15 million USD using an affiliate program.
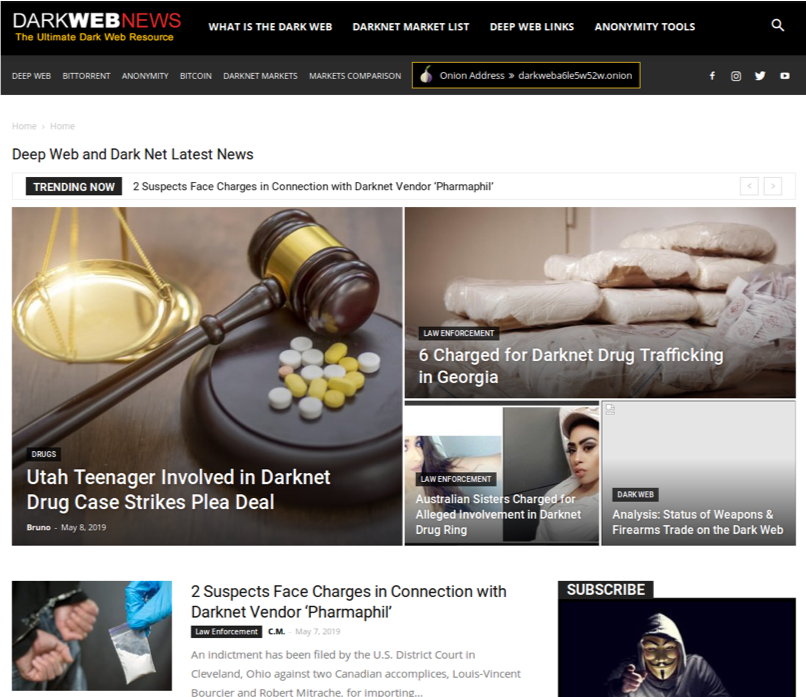
Darknetmarket.com was another example of a page similar to deepdotweb that was shut down. The content was very similar: links to dark markets, tutorials, news about the Darknet. It was available both by TOR and by normal www website. The last piece news came on May 6th – the day when deepdotweb was seized by the FBI. For the following 2 days the website was available, but there was no new information. That silence seemed out of the ordinary, at the very least a comment on the DDW case was expected since the portal was its direct competitor. On the third day, May 9th, the website stopped working and till today it shows nothing, neither seizure information, nor typical content. On the same day, their official Twitter account showed the last tweet:

This screen is taken from google cache, because the Dark Web News account on Twitter doesn’t exist anymore.
The last screenshot made by archive.org on 9th May before it was disabled. Dark Web News was online since 2014
There were also darknetmarkets.co and darknetmarkets.com that went offline and stopped working without any explanation.
Cannabis Growers & Merchants Co-op (CGMC), a darknet market in TOR; specialized only in drugs stopped operating on May 12th. That was the fourth dark market that stopped working over the last two months. It was probably another consequence of the last LE seizures. It’s possible that the owners will try to disappear, and then return after strengthening their security. They want to be sure that nobody is threatening them anymore, so it’s possible that they would return under another brand, which would make it difficult for LE to connect with the previous brand (CGMC). The most curious particularity about this case is that CGMC made such a sudden exit, yet there was no scam which is very common in these scenarios. They did not steal anything and even returned money to all the vendors. That is why some vendors call it “the nicest exit” of a dark market that there’s even been.
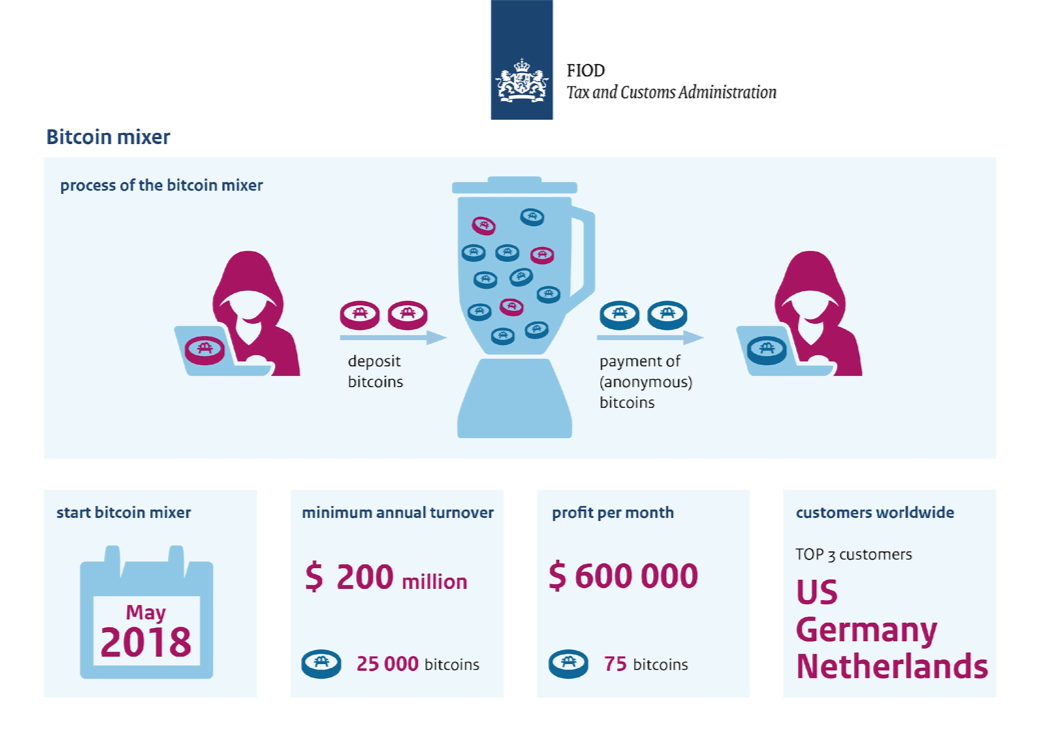
On May 22nd, Dutch LE announced a seizure of one of three biggest BTC mixers – bestmixer.io. Because BTC is the most popular cryptocurrency and it is not anonymous, mixing services play a crucial role in money laundering for Darknet players. Anybody who has suitable skill can trace BTC flow across its path. Mixer makes it possible to conceal the origin or destination of BTC. Bestmixer.io service was used to split up cryptocurrencies (BTC, Litecoins, Bitcoin Cash and Ethereum) after which they are mixed together in a different combination.
Dutch LE claims they gathered lots of information about transactions processed by bestmixer.io. Depending on the amount of detail regarding transactions that services stored, this could be an important step towards fighting cybercriminals. It is possible that thanks to this success, LE will catch more various types of criminals, not only from the Darknet. As bestmixer.io has only operated for a year, the aftermath won’t be a disaster.
Bestmixer summary. Source: www.fiod.nl/the-fiod-and-the-public-prosecution-service-take-money-laundering-machine-for-cryptocurrencies-offline/
Currently, many dark market-related websites on TOR have problems with DDoS. At the beginning of this post I mentioned Dream Market, but there are quite a few more examples. Dread forum, Reddit equivalent in the Darknet, was inaccessible for several days in May. Because of all the other events, there was speculation that Dread was seized as well. Dread came back online on May 20th, but it seems that there are going to be next DDoS attacks in the nearest future.
Other popular darknet markets are under ongoing DDoS attack too. For example Nightmare Market and Empire Market. Berlusconi Market has an issue with availability, but we are still not sure if it is due to DDoS.
There is no certainty who is behind all these DDoS attacks. It could be law enforcement wanting to destroy all dark markets or hackers simply seeking ransom. That last issue occurred in the Dream Market case and it was confirmed by Dream administrators. It is certain that those attacks introduced another element of uncertainty in the Darknet environment.
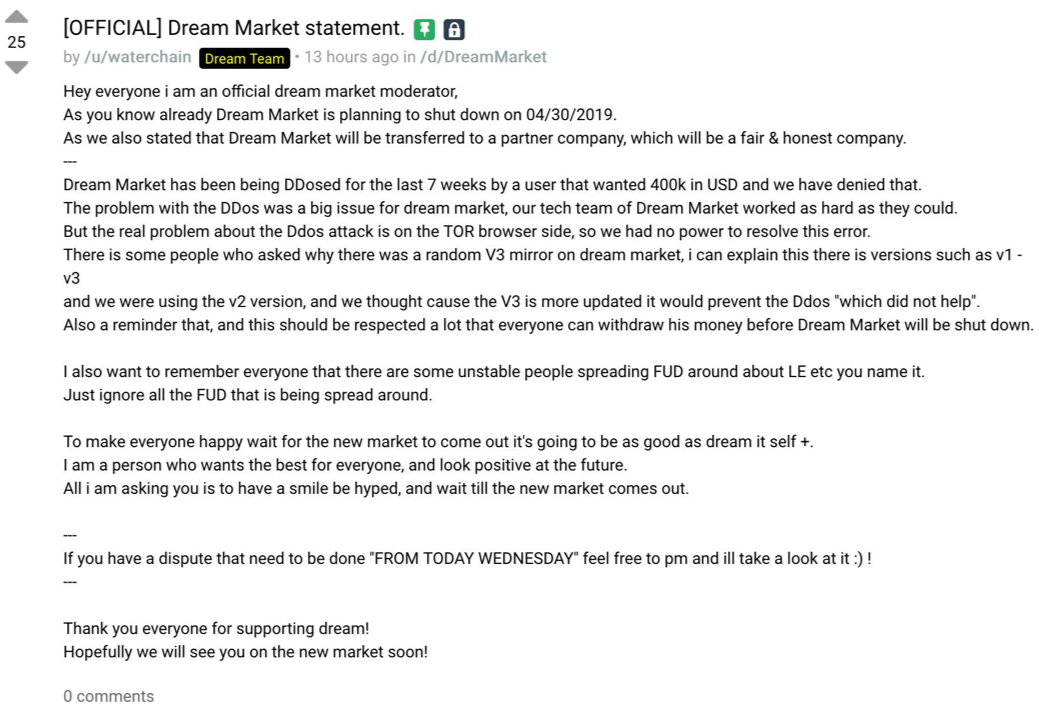
Dream Market moderator statement about their DDOS and ransom problems. Reddit, 28th March:
Right now, dark markets in TOR’s part of Darknet face the biggest problem since AlphaBay and Hansa fell in 2017. For some younger Darknet users, it can be terrifying, but older players kept saying relax, wait for the dust to settle. A big gap in the market appeared and it will be filled by new dark markets that will arise soon.
For sure, some of the markets will be scammers lurking for inexperienced Darknet users and some will be run by LE itself, like it was in Hansa Market case or Carder Profit forum case, which was operated from the start by the FBI. Others, like Libertas Market on May 23rd, will transfer to another part of the Darknet not connected with TOR (like I2P). The most well-known vendors will be selling their merchandise through their private channels, like their own shops in the Darknet, social media or e-mails.
It is certain that it isn’t the end of dark markets. Its growth has been temporarily suspended but will soon move forward again. The big unknown, for now, is the aftermath of bestmixer.io being seized.
From a business perspective, one thing is probable – in the nearest future, the price of stolen data, credit cards, firearms, drugs, malicious software, hacking tools, access device-making equipment, and other illegal contraband will partly increase. The more dark markets dealing with illicit goods are shut down, the less supply of those stolen goods and services there will be on the Darknet. And since demand for i.e. stolen virtual credit has increased, the average price for that type of cards will go up… till the dust settles.
In the last website seizures (WSM and DDW) the central part was played by J-CODE, coordinated by the US Department of Justice3 operation which targets drug trafficking on the Darknet. Its full name is Joint Criminal Opioid and Darknet Enforcement. The operation was announced in January 2018 and during just a year they made great strides. If they continue to work with the same engagement, more dark markets may fall, especially those that concentrate on drugs.
Right now it seems that dealing with drugs is a crucial goal in the process of fighting with dark markets, especially for the US LE. What is their plan for other illegal goods and services, i.e. stolen credit cards and personal data? On the other hand, we have to remember that a big part of stolen credit card vendors is not based in English-speaking countries, they come from the former USSR region. The US and European LE don’t have enough reach to work in most of the Russian speaking states.
Due to the reasons stated above, the last LE activity probably won’t have a huge impact on the stolen credit card market. Some well-known distribution channels were cut, but most of the carding environment still continues to work as usual.
A Distributed Denial of Service (DDoS) attack is an attempt to make an online service unavailable by overwhelming it with traffic from multiple sources. They target a wide variety of important resources, from banks to news websites, and present a major challenge to making sure people can publish and access important information. Source: www.digitalattackmap.com/understanding-ddos/
↩
Darknet is an umbrella term describing the portions of the Internet purposefully not open to public view or hidden networks whose architecture is superimposed on that of the Internet. All Darknets require specific software installed or network configurations made to access. In the article by “Darknet” in most cases I am referring to TOR – the most popular Darknet. Another popular type of Darknet are I2P and Freenet.↩
Many US federal institutions take their part in J-CODE apart of Department of Justice: FBI, Drug Enforcement Administration, U.S. Postal Inspection Service, U.S. Customs and Border Protection, U.S. Immigration and Customs Enforcement Homeland Security Investigations, Department of Defense and Financial Crimes Enforcement Network.↩